NetFlow is Everywhere. Intelligence is Not.
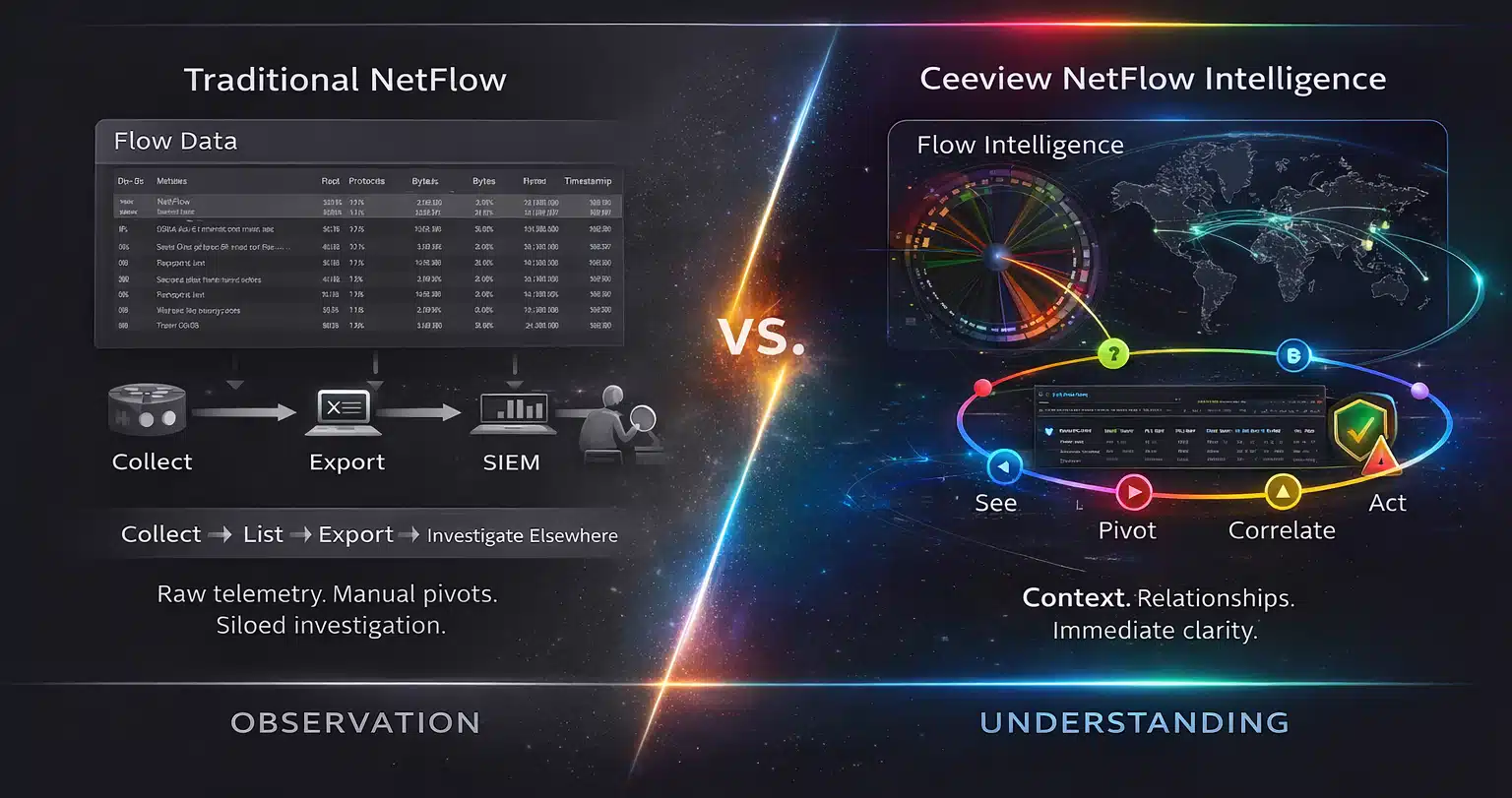
Most NetFlow tools collect telemetry and export it somewhere else for analysis.
That leaves operators jumping between dashboards, SIEM tools, and spreadsheets just to understand what’s happening on the network.
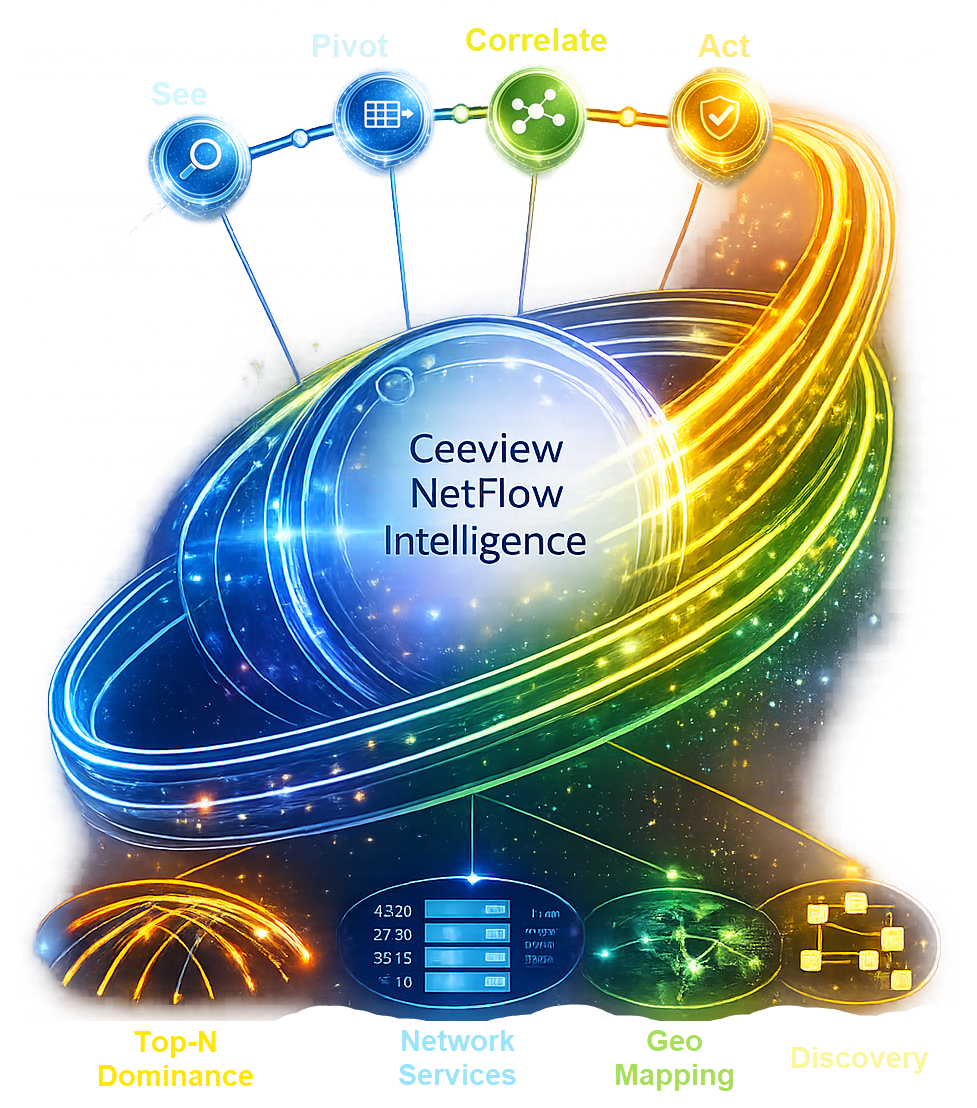
Ceeview NetFlow Analyzer transforms raw flow data into contextual intelligence — giving teams immediate visibility into traffic relationships, anomalies, and dominant network consumers directly within a single operational console.
As part of the Ceeview Intelligent Observability Platform, NetFlow telemetry becomes actionable operational and security intelligence — enabling investigation without exports, pivots, or tool switching.
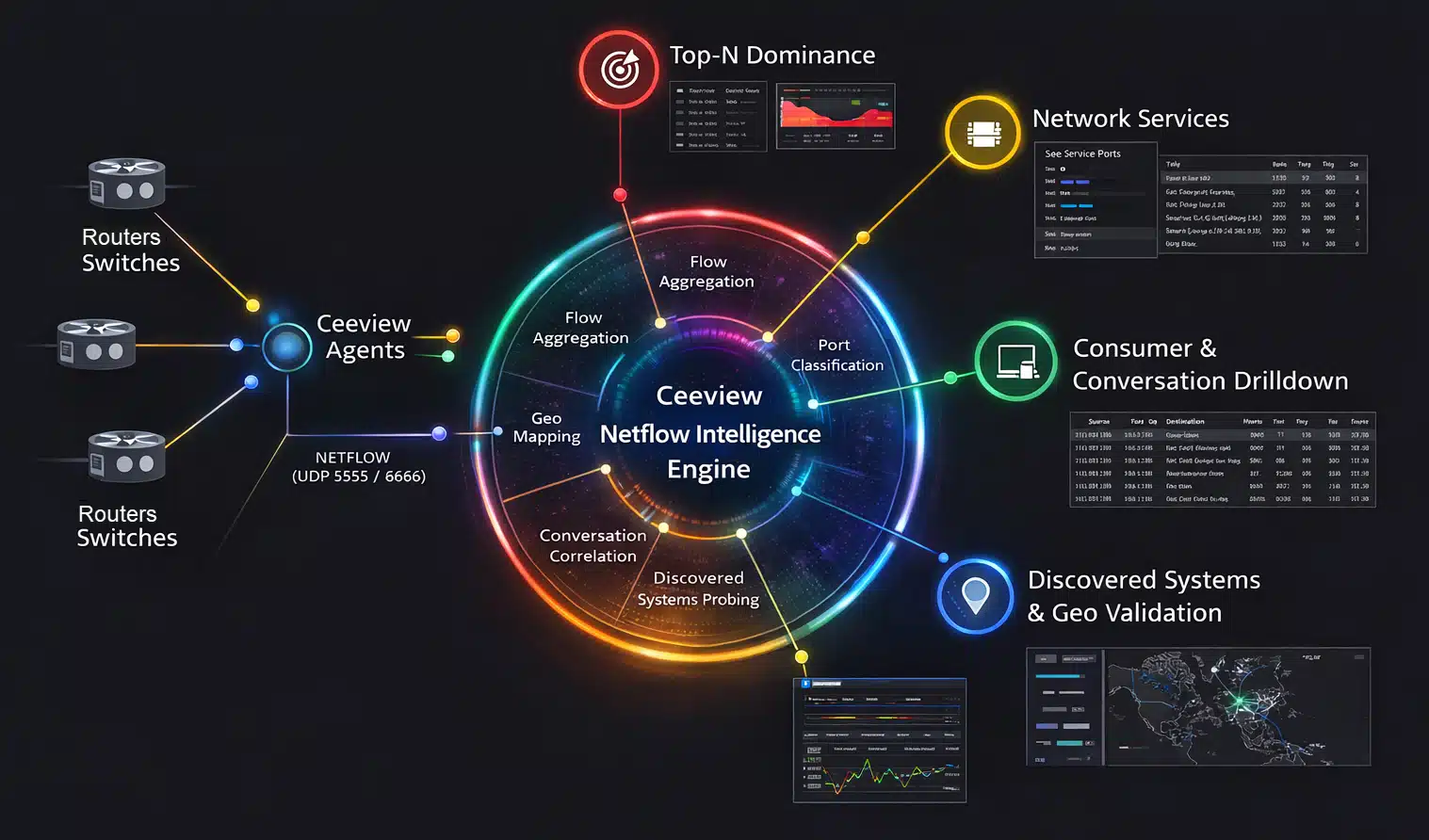
Ceeview NetFlow Intelligence Engine
Ceeview processes network flow telemetry through the NetFlow Intelligence Engine, transforming raw records into contextual insight.
Flow data from routers and switches is aggregated, classified, and correlated to expose traffic relationships across systems, services, and endpoints. Dominant consumers surface instantly, conversations can be drilled down to session detail, and unknown external systems are automatically discovered and validated.
The result is a live operational view of how your network actually behaves — enabling teams to investigate anomalies, understand service dependencies, and trace traffic across the enterprise without exporting data or leaving the platform.
NetFlow Intelligence in Action
As highlighted by MSPs and Enterprises running Ceeview in production, the power of NetFlow intelligence lies in turning raw telemetry into immediate operational insight. The workflows below demonstrate how teams investigate anomalies, identify dominant consumers, validate potential threats, and understand traffic relationships — all from a single operational console.
“I’ve used a lot of NetFlow tools over the years, and I’ve never seen one deliver this level of granular, usable, actionable data this quickly. Ceeview went deep into the data and made it truly visible and usable — it’s heads and shoulders above most NetFlow products on the market today."

Unnar Thor Gardarsson
CEO, ConnectOn
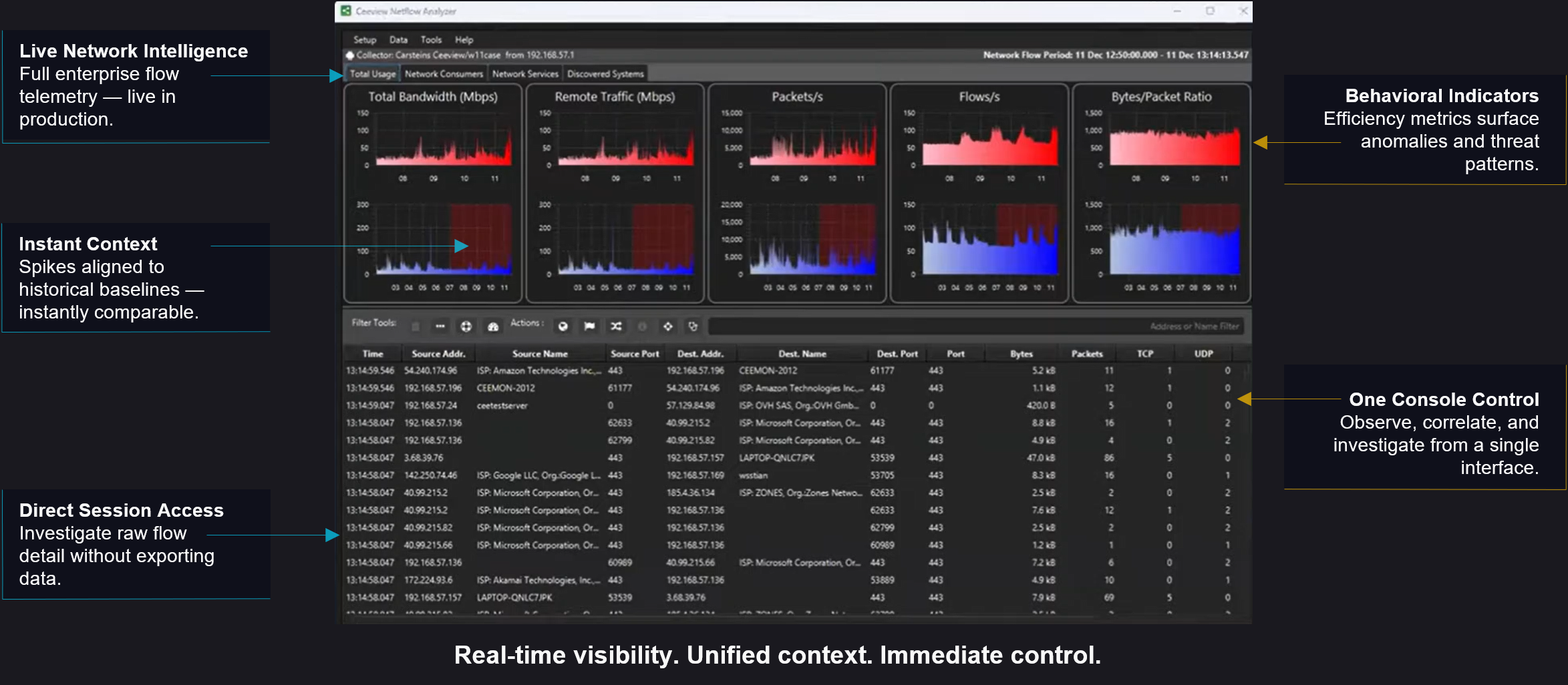
Start With Instant Network Situational Awareness
Total Usage Console
Every investigation begins with understanding what the network is doing right now.
Ceeview’s Total Usage Console provides an immediate view of live enterprise flow telemetry — revealing bandwidth utilization, packet activity, flow rates, and traffic composition across the environment. Time-based charts highlight sudden changes in traffic behavior, helping operators quickly recognize unusual activity.
From this single operational view, teams can immediately identify abnormal patterns and drill directly into session-level flow records to investigate specific conversations without exporting data or switching tools.
This instant situational awareness provides the foundation for deeper investigation into traffic consumers, services, and potential security threats.
From this starting point, operators can pivot directly into traffic consumers, service analysis, and threat investigation workflows.
Identify Dominant Traffic Consumers
Instant Top-N Intelligence
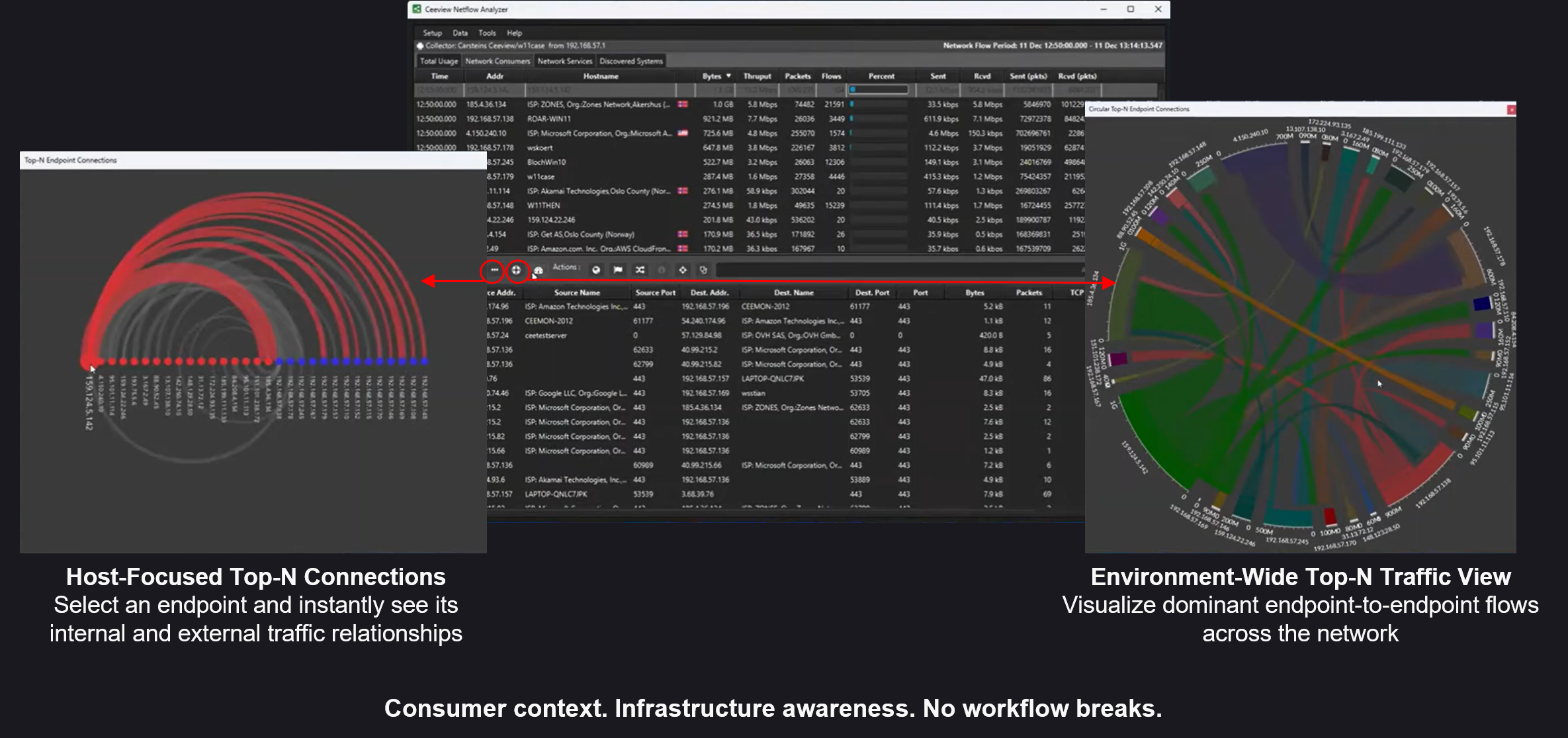
With overall network activity visible, the next step is identifying which systems are responsible for generating the most traffic.
Ceeview instantly surfaces dominant endpoints directly from the live NetFlow dataset, ranking internal and external systems by bandwidth consumption, packet activity, and flow volume. This Top-N view allows operators to immediately identify the hosts driving network behavior without exporting telemetry or building custom reports.
Selecting any endpoint reveals its traffic relationships across the environment, showing both internal communications and external destinations. Visualizations expose how heavily connected systems interact across the network, helping investigators quickly understand traffic dominance and dependency patterns.
From this vantage point, teams can quickly determine not only which systems dominate network activity, but also where their traffic is flowing — providing a natural pivot into geographic traffic analysis and deeper conversation investigation.
Visualize Global Traffic Relationships
Geographical Connection View
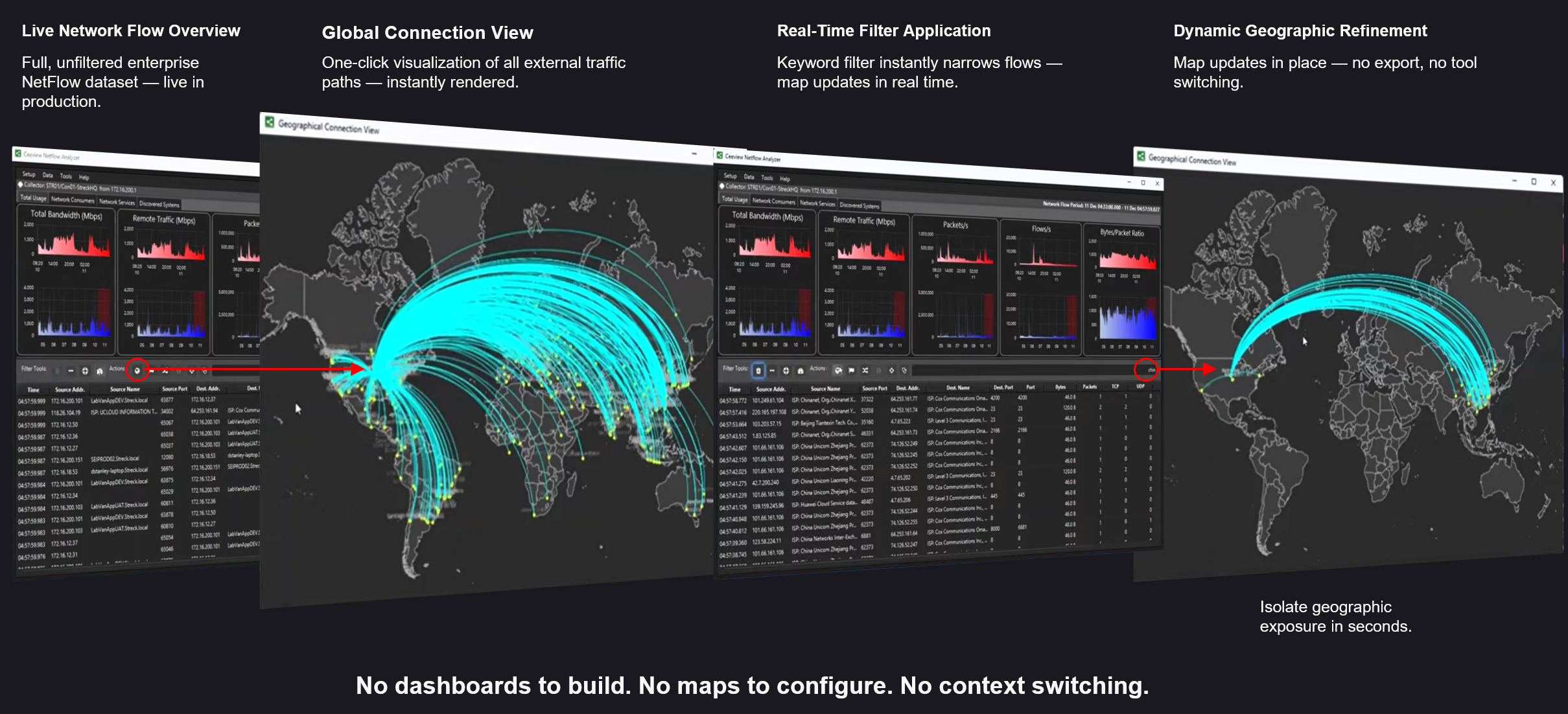
Once dominant traffic systems are identified, the next step is understanding where their traffic is going. Ceeview’s Geographical Connection View renders external network flows on a global map, instantly revealing how internal systems communicate with endpoints across the internet.
Each connection is derived directly from the live NetFlow dataset, allowing operators to visualize geographic traffic patterns without building dashboards or exporting data.
From the Total Usage Console, investigators can pivot directly into the geographic view to explore external communication paths. As filters are applied to narrow the dataset, the map updates dynamically — isolating specific hosts, destinations, or traffic patterns in real time.
This capability makes it easy to identify unexpected geographic exposure, investigate suspicious external connections, and quickly understand the global footprint of network activity.
From here, investigators can drill further into the specific conversations and flow records responsible for the observed activity.
Trace Traffic Conversations to Their Source
Consumer-Led Traffic Intelligence
Once geographic traffic patterns are understood, investigators can drill into the specific conversations responsible for that activity.
Ceeview enables consumer-led traffic analysis directly from the NetFlow dataset, allowing operators to follow network activity from dominant systems down to individual flow exchanges. Traffic can be filtered by infrastructure interface or logical network path, helping teams isolate activity within specific segments of the environment.
From there, investigators can pivot into summarized geographic traffic views and quickly narrow the dataset to the destinations responsible for the observed activity. Selecting any entry reveals conversation-level flow records, exposing packet counts, byte volumes, ports, and timing details for each communication session.
Ceeview also enriches these records with endpoint context where available, including organization ownership, ISP information, and geographic region. This allows operators to quickly determine whether a connection represents expected service behavior or something that requires further investigation.
By maintaining the full investigative workflow inside a single interface, teams can move seamlessly from dominant traffic consumers to precise conversation details without exporting data or switching tools.
Validate Suspicious Traffic Behavior
From Raw Flow Data to Validated Threats in Minutes
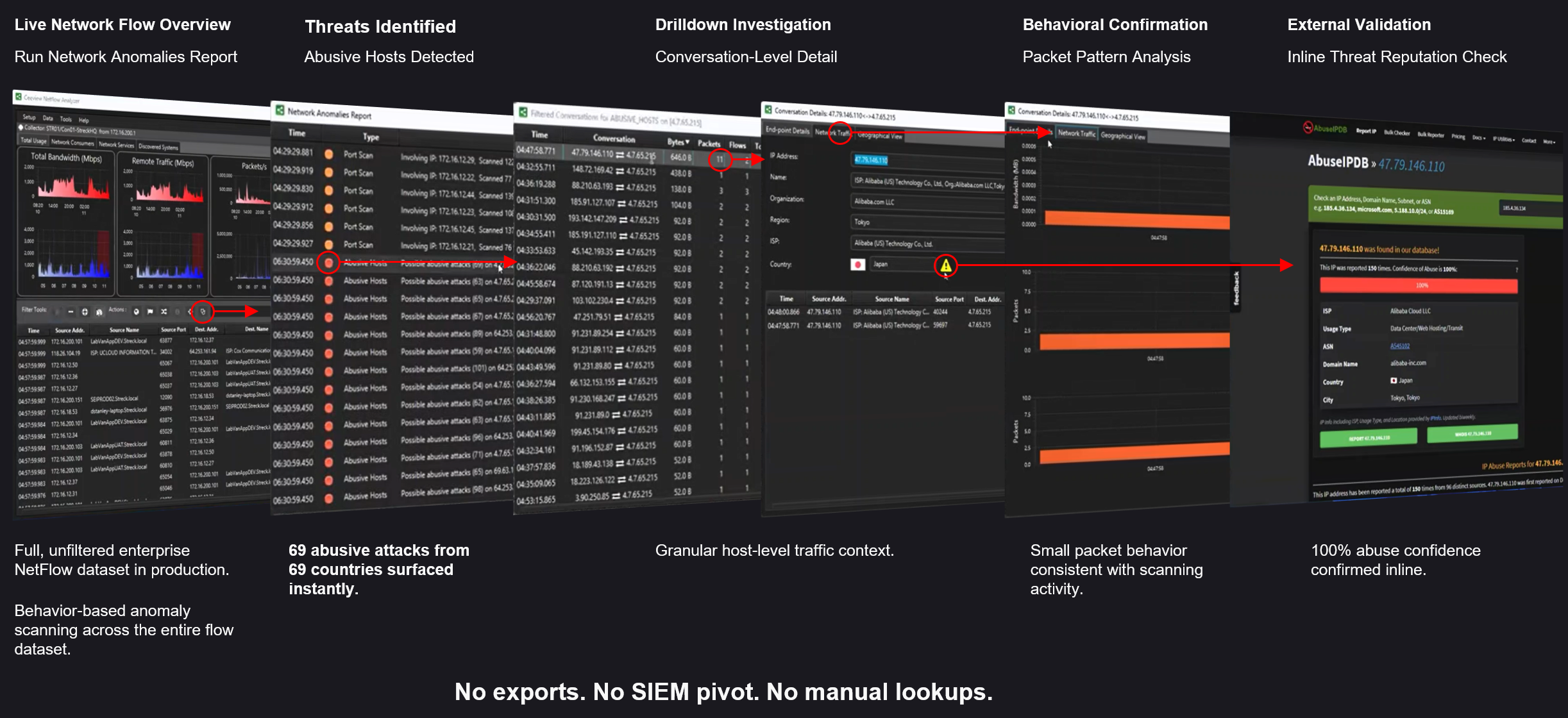
Once suspicious conversations are identified — often surfaced through Ceeview’s anomaly detection analysis — investigators need to determine whether the observed behavior represents a legitimate service interaction or a potential security threat.
Ceeview allows operators to move directly from flow analysis to behavioral validation by examining detailed traffic patterns within the NetFlow dataset. Conversation-level flow records expose packet counts, byte volumes, ports, and communication timing, making it possible to recognize behaviors commonly associated with scanning activity, command-and-control communication, or other anomalous traffic patterns.
From the same investigative workflow, suspicious endpoints can be checked against external reputation intelligence to determine whether an address has been previously associated with abusive or malicious activity. This allows operators to quickly confirm potential threats without exporting telemetry to separate security platforms.
By combining anomaly detection, behavioral analysis, and inline threat validation, Ceeview enables teams to move from raw flow telemetry to confirmed security insight within minutes — all while maintaining the full investigative context of the original traffic analysis.
From here, investigators can pivot into service-level traffic intelligence to understand which applications or protocols are responsible for the observed behavior.
Understand Service-Level Traffic Behavior
Network Services Traffic Intelligence — Pivot by Port in Seconds
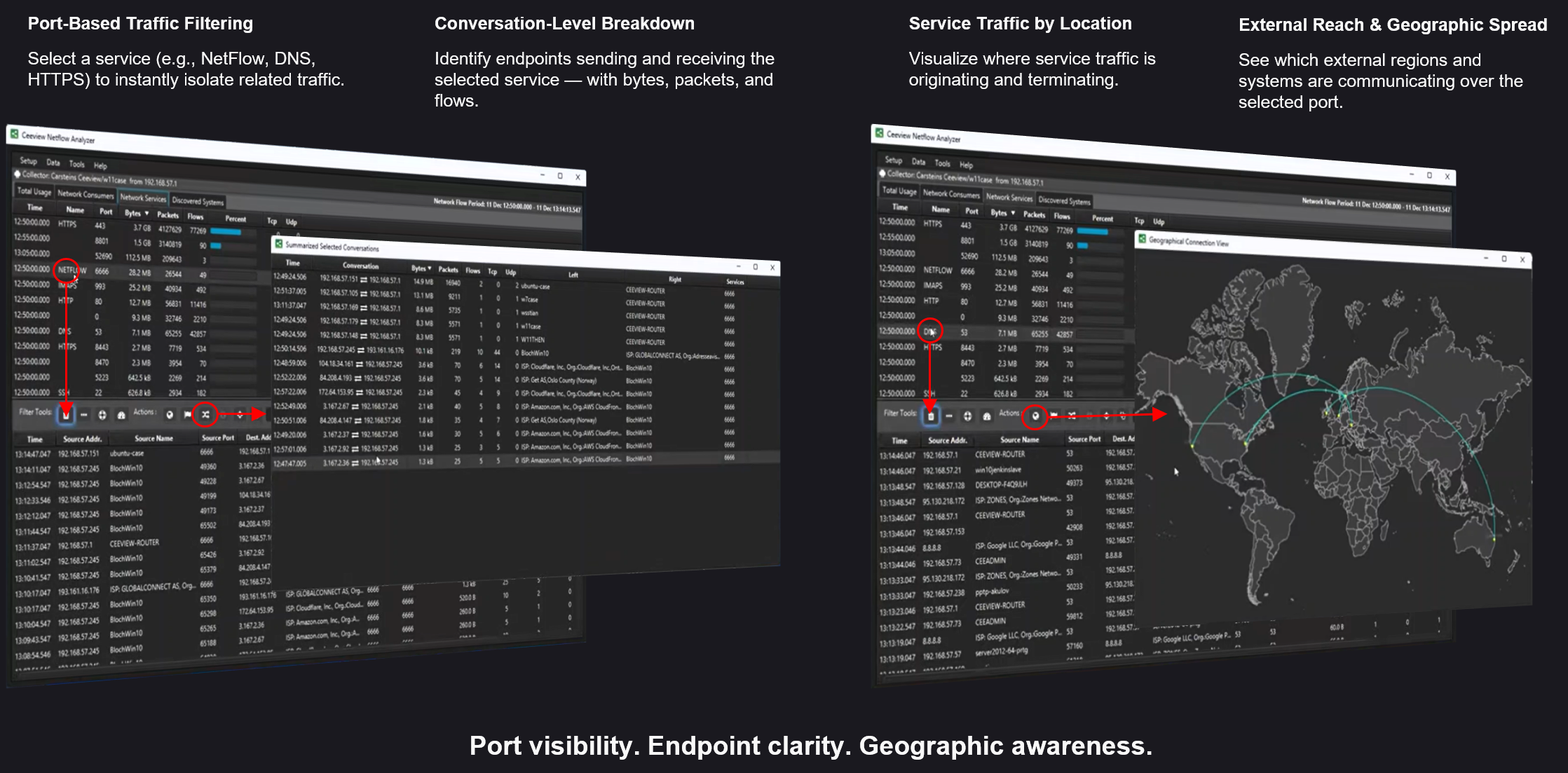
Once suspicious traffic behavior is validated, the next step is understanding which applications or services are responsible for generating the activity.
Ceeview allows investigators to pivot directly from endpoint conversations into service-level traffic analysis by filtering the NetFlow dataset by port or protocol. This instantly isolates traffic associated with specific services such as HTTPS, DNS, database connections, or other application protocols.
From this view, operators can examine conversation-level activity for the selected service, revealing which endpoints are sending and receiving traffic, how much data is being exchanged, and how frequently the service is being used across the environment.
Service intelligence can also be visualized geographically, allowing teams to quickly understand where service traffic is originating and which external regions or systems are interacting with the application.
By combining port-level filtering, endpoint visibility, and geographic traffic insight in a single workflow, Ceeview enables investigators to rapidly understand how critical services are being used across the network.
From here, investigators can pivot to automatic endpoint discovery to identify the external systems involved in those communications.
Identify External Systems Automatically
Automatic Endpoint Discovery — Know Who You’re Talking To
As investigations progress, analysts often encounter unfamiliar external IP addresses within the NetFlow dataset. Understanding who these systems belong to is critical for determining whether traffic represents legitimate service usage or potential risk.
Ceeview automatically discovers and resolves external systems observed in network flows, enriching IP addresses with organizational ownership, geographic location, and related endpoint information. This intelligence is derived directly from live traffic analysis, allowing investigators to immediately understand the identity and origin of systems communicating with their network.
Discovered endpoints can be explored directly within the NetFlow Analyzer interface, where investigators can review associated conversations, examine traffic patterns, and trace how those systems interact with internal infrastructure.
For additional context, discovered systems can be opened in the Geographical Connection View, allowing teams to instantly visualize where communications originate and terminate across the global network.
By automatically resolving and geo-validating external systems within the flow dataset, Ceeview eliminates the need for manual IP lookups or external enrichment tools — allowing investigators to maintain full investigative context from discovery through resolution.
Turn Network Flow Data Into Operational Intelligence
Traditional NetFlow tools collect enormous volumes of telemetry but often leave operators to manually piece together what the data actually means.
Ceeview transforms raw NetFlow telemetry into contextual operational intelligence — enabling teams to observe network behavior, investigate anomalies, trace conversations, validate threats, and understand service interactions from a single operational console. NetFlow data provides deep visibility into traffic patterns and communication behavior across the network, helping administrators analyze and optimize infrastructure performance.
Instead of exporting data between tools, building dashboards, or performing manual lookups, Ceeview keeps the entire investigation workflow connected — allowing analysts to move seamlessly from high-level visibility to conversation-level insight and endpoint attribution.
The result is faster investigations, clearer operational understanding, and more confident decisions about network behavior.
See the NetFlow Intelligence Engine in Action
The workflows demonstrated throughout this page come directly from the Ceeview NetFlow Analyzer, presented by Ceeview CTO Carstein Seeberg at the Ceeview User Conference.
Watch the full presentation to see the NetFlow Intelligence Engine in action, or explore the two-page overview to quickly understand how Ceeview transforms raw flow telemetry into actionable operational insight.
Both resources highlight how operators can move from raw network flow data to meaningful investigation and understanding in minutes.
Experience Ceeview NetFlow Intelligence
Ceeview NetFlow Control is part of the Ceeview Intelligent Observability Platform, where network telemetry, infrastructure visibility, service intelligence, and operational analytics converge into a single platform.
If your organization relies on NetFlow for network visibility, Ceeview enables you to go beyond observation — turning flow telemetry into actionable intelligence for operations, performance analysis, and security investigations.
Request a demo to see how Ceeview NetFlow Intelligence can transform the way your team understands network behavior.
Contact us for more info
Gain instant insight into network traffic behavior with Ceeview NetFlow Intelligence. Detect anomalies, investigate conversations, understand service interactions, and identify external systems from one operational console. Ready to transform how your team analyzes network activity? Contact us for a demo today.
Orange

Visma

Proff

Luftfartstilsynet

Infront

Streck

Gassco

ConnectOn

Stadt Zurich

ARCO

Sopra Steria

Acentix